Turning the Tables on Restaurant Reservation Fraud
How reservation apps can put fraudsters in a to-go box
How reservation apps can put fraudsters in a to-go box
A restaurant reservation can make or break someone’s evening, even someone’s week if they identify as a “foodie.” Fraudsters, of course, are well aware and have found a way to juke reservation apps and naive consumers who mistakenly believe they’re in for the Michelin Star treatment at that hard-to-get-into restaurant.
Sit-down eateries have long been fertile ground for fraud (dine-and-dashing, running the card twice in the back, hacking users through malicious QR codes), but restaurant reservation fraud—akin to ticket scalping—uniquely impacts reservation platforms, restaurants, and their would-be patrons.
Let’s take a closer look at reservation fraud and how to stop bad actors from feasting on reservation apps.
A maître d’s worst nightmare
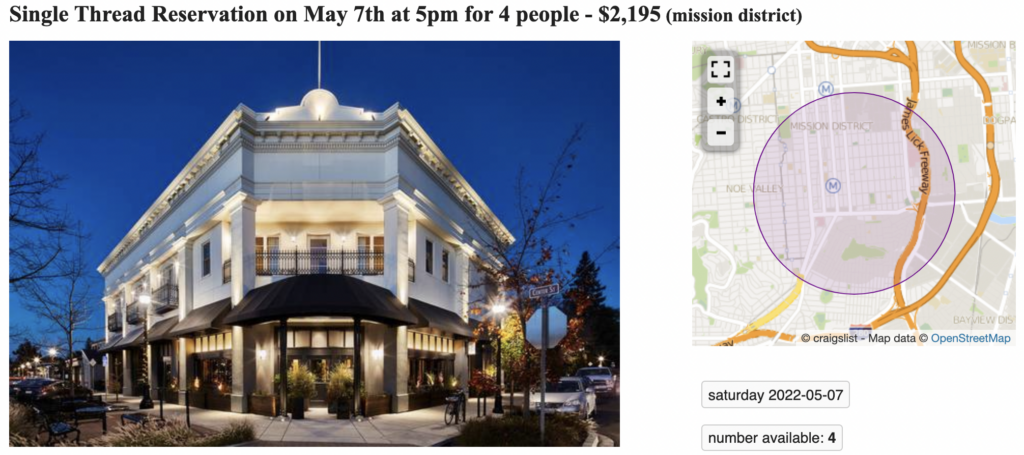
After scammers land a restaurant reservation—typically at a ritzier establishment—they attempt to sell it on Craigslist, Facebook Marketplace, and other classifieds. The poster withholds vital information from unsuspecting buyers: other folks have purchased the same reservation.
Imagine showing up for your anniversary dinner only to find four other parties have the same reservation—a party of ten with no table and no backup plan.
Duped customers are left with hurt feelings and empty stomachs, but restaurants, many still finding their footing amid the pandemic, suffer lost revenue and the likelihood that neither of these customers will return in the future. In turn, the restaurant blames the reservation app and may seek out a similar platform that isn’t so easily manipulated.
Does such a platform exist? How can reservation apps (and restaurants) turn the tables on bad actors?
Tonight’s special: preemptive fraud detection
Deduce recently partnered with a global restaurant reservation platform to solve its reservation fraud issue. The intelligence, scalability, and preemptive nature of Deduce’s solution was precisely what the app needed to put fraudsters in a doggy bag.
Malleability played a crucial role as well. Deduce created custom risk signals and provided a continuous authentication solution for the app, Improbable Travel, to neutralize phony reservation bookers. If someone in Kansas makes reservations at restaurants in New York, Los Angeles, and New Orleans for the same day, chances are it’s a ruse, doubly so for new accounts. By flagging such cases based on geolocation and account status, and referring them to the reservation app for manual review, Deduce’s tailor-made approach reserved restaurant tables for legitimate customers only.
A recipe for success
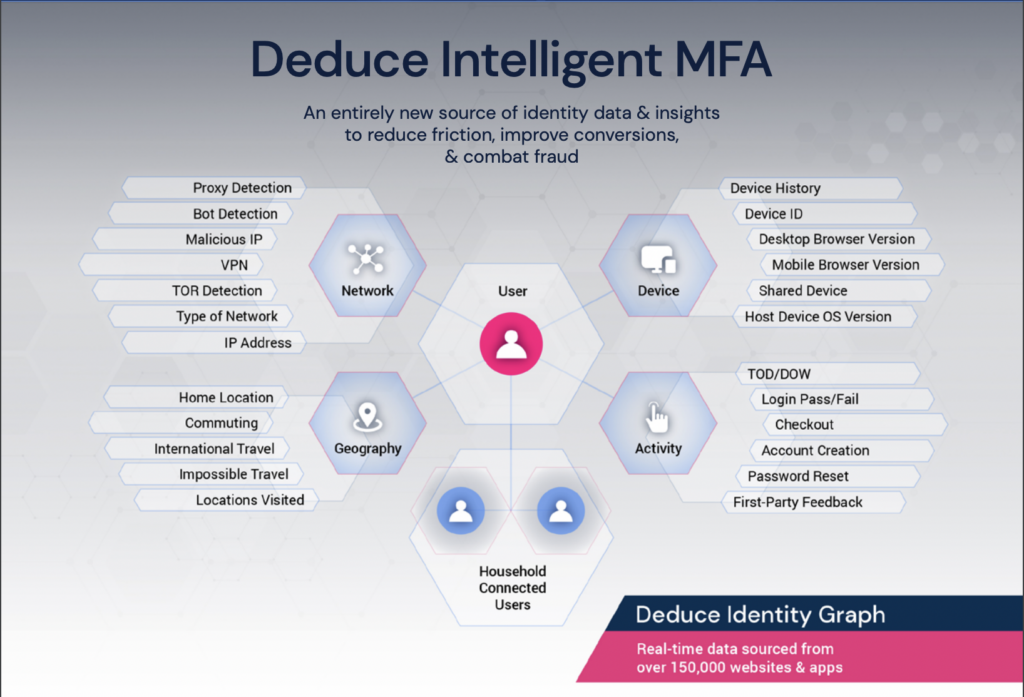
Deduce owes its flexibility and real-time fraud detection to its Identity Network comprising 500 million anonymized user profiles, gleaned from over 150,000 websites and apps, and over 1.4 billion daily activities. In fact, Deduce sees the majority of the transactional online U.S. population multiple times per week. It verifies users through risk signals, like Impossible Travel, and trust signals such as familiar device, familiar network, familiar activity, and familiar time of day.
These real-time risk and trust signals work in tandem to spot bad actors long before any malicious behavior can take place. In the case of a restaurant reservation platform, preemptively intercepting fraud is the way to a restaurant and app user’s heart: full tables, satiated appetites, less churn.
Are you starving for an effective first line of defense against account creation fraud and to prevent ATO attacks while reducing friction for legitimate customers? Contact us today and get set up in just a few hours.